Reference no: EM13854628
Question 1: Network Design
Consider a square area of 100m x 100m. You want to detect the presence of rodents (say rats) in this area using Mica 2 motes equipped with a motion detector whose range is 2m and powered by a 2000 mAh battery. Each mote with its sensor board costs 100 USD. The table below lists the power consumption and other attributes for for various activities for the mica mote.
| Component/Activitiy |
Rate |
Startup Time |
Current Consumption |
| MCU active |
4 MHz |
N/A |
5.5mA |
| MCU idle |
4 MHz |
1 �s |
1.6mA |
| MCU suspend |
32 kHz |
4ms |
<20 �s |
| Radio transmit |
40 kHz |
30 ms |
12 mA |
| Radio receive |
40 kHz |
30 ms |
1.8 mA |
| Photoresister |
2000 Hz |
10 ms |
1.235 mA |
| Motion detector |
100 Hz |
10 ms |
5 mA |
| Accelerometer |
100 Hz |
10 ms |
5 mA/axis |
| Temperature |
2 Hz |
500 ms |
0.150 mA |
Your monitoring application should run continuously for 6 months. Every time a rat is detected a message should be sent to a server (through gateway(s)).
Describe a solution to this problem: discuss node placement, choice of gateway(s), sensing strategy, routing strategy, duty cycling and the cost of your solution. Also explicitly state all assumptions that you make.
Question 2: Security
Due to the lack of a centralized authority, it is not easy to manage node identity in large-scale networks. One possible attack is for an attacker to capture nodes in the network, duplicate their identities (including secure credentials), and insert them back into the network. The attacker will then be able to launch other attacks using the replicated/fabricated nodes. Propose a solution to detect such node replication attacks. You must clearly outline your protocol in detail and state all assumptions. Including an illustrative example demonstrating your solution is also strongly recommended.
Question 3: Routing
Fig. shows a network topology, where Node S is the source node and Node D is the destination node. A 0 to 1 number beside an arrow shows the link quality Packet Reception Rate (PRR) of an asymmetric wireless link; for example, the PRR from Node a to D is 0.9 (90%). The numbers inside the brackets beside a node is the X, Y co-ordinates of a node; for example, the coordinates of Node c is (1, 2).
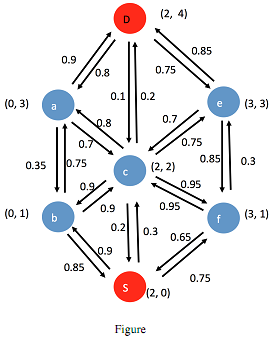
(a) If the nodes run Collection Tree Protocol (CTP) that uses expected number of transmissions (ETX) as routing metric. What is the path between Nodes S and D? What is the path ETX?
(b) If the nodes run Greedy Perimeter Stateless Routing (GPSR), assumed the radio range of a node is p2, what is the path between Nodes S and D? Note that GPSR assumes circular link model and does not take link quality into account.
Question 4: Outlier detection
Fig. shows the two-dimension values of 10 sensors. What are the Local Outlier Factor (LOF)1, LOF3, and LOF5 of Nodes 1, 3, 5, 7, 9?
The sensor values of the nodes are:
| Node ID |
X |
Y |
| 1 |
116 |
91 |
| 2 |
91 |
102 |
| 3 |
99 |
136 |
| 4 |
107 |
116 |
| 5 |
75 |
91 |
| 6 |
79 |
87 |
| 7 |
231 |
172 |
| 8 |
255 |
219 |
| 9 |
203 |
206 |
| 10 |
190 |
223 |
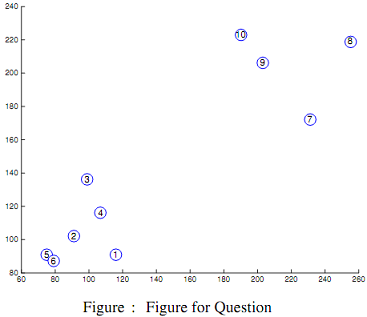
|
Applications for small businesses
: You are a marketing executive for a software development company that produces accounting applications for small businesses. Your company wants to expand internationally and has identified two countries for its first venture.
|
|
Why might a mutation in the coding sequence of a gene
: Why might a mutation in the coding sequence of a gene result in a genetic, but not a phenotypic polymorphism? Probing for a particular exon may identify multiple sites in the genome. Why?
|
|
The primary weakness of ebit-eps analysis is that
: The primary weakness of EBIT-EPS analysis is that
|
|
Types of fraud impacting financial statements
: Internal control is a plan of organization and system of procedures implemented by company _____ and the _____ designed to accomplish five objectives.The two most common types of fraud impacting financial statements are
|
|
What is the path between nodes s and d
: Describe a solution - discuss node placement, choice of gateway(s), sensing strategy, routing strategy, duty cycling and the cost of your solution. Also explicitly state all assumptions that you make.
|
|
Compute the bond interest expense for the first six months
: Compute the bond interest expense for the first six months of 2012, using the interest method. Show how the $1,400,605 price must have been determined.
|
|
Records revealed the following reconciling items
: The cash account for Meers Medical Co. at November 30, 2015, indicated a balance of $14,470.19. The bank statement indicated a balance of $14,363.84 on November 30, 2015. Comparing the bank statement and the accompanying canceled checks and memora..
|
|
Contrast role of promotion in an international public accoun
: consider pricing from a strategic rather than a tactical perspective
|
|
Demonstrate your knowledge of finance theory
: To demonstrate your knowledge of finance theory, be sure to include your personal thoughts on the subject.
|