Reference no: EM13767771
Global Finance, Inc. Network Diagram
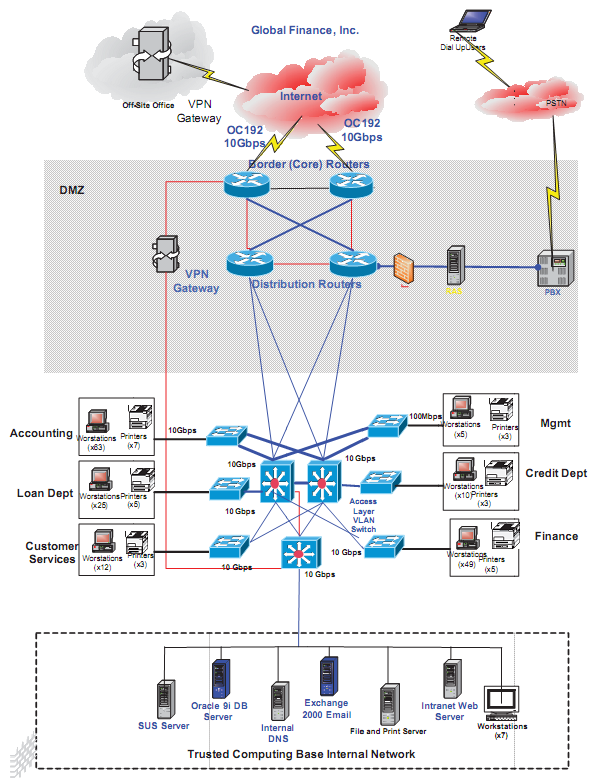
Above is the Global Finance, Inc. (GFI) network diagram. A hypothetical company, GFI has grown rapidly this past year and implemented a number of network devices as displayed in the diagram. The company invested in the network and designed it to be fault tolerant and resilient from any network failures. However, although the company's financial status has matured and its network has expanded at a rapid pace, its overall network security posture has not kept up with the company growth.
GFI's network has historically been fairly stable, and the company has not experienced many full scale network outages. GFI has hired three (3) network engineers to keep up with the network growth, as well as the bandwidth demand by the company employees and the clients. However, the company has not hired any security personnel who can take care of the operational security responsibility.
The trusted computing base (TCB) internal network within the Global Finance, Inc. Network Diagram hosts the company's mission critical systems that are vital to the company's operations that also affect the overall financial situation. The Oracle database and email systems are among the most intensively used application servers in the company. GFI cannot afford system or network outages, as its cash flow and financial systems heavily depend on the network stability and availability. GFI has experienced DoS network attacks twice this year, and its Oracle database and email servers had been down for a total of one (1) week as a result. The recovery process required GFI to utilize $25,000 to restore its operations to the normal operating baseline. GFI estimated the loss from these network attacks at more than $1,000,000, as well as lost customer confidence.
Write a eight to ten (8-10) page formal risk assessment proposal in which you:
1. Describe the company network, interconnection, and communication environment.
2. Assess risk based on the GFI, Inc. network diagram scenario. Note: Your risk assessment should cover all the necessary details for your client, GFI Inc., to understand the risk factors of the organization and risk posture of the current environment. The company management will utilize this risk assessment to determine what actions to take; therefore, it must be comprehensive for the business leaders to make data-driven decisions.
a. Defend your assumptions where pertinent information from the scenario isn't available.
b. Ascertain apparent security vulnerabilities, and analyze at least three (3) such vulnerabilities. Such analysis should entertain the possibility of faulty network design. Recommend mitigation processes and procedures for each of the identified vulnerabilities.
c. Justify your cryptography recommendations, based on security concerns and requirements, data-driven decision-making, and objective opinions.
3. Examine whether your risk assessment methodology is quantitative, qualitative, or a combination of these, and discuss the main reasons why you believe that the methodology that you utilized was the most appropriate.
4. Explain the way in which you would present your findings and assessment to the company's management and thus facilitate security buy-in and concentration.
5. Using Microsoft Visio or its open source equivalent, redraw the CFI diagram, depicted as a secure and risk-mitigating model. Note: The graphically depicted solution is not included in the required page length.
6. Use at least three (3) quality resources in this assignment. Note: Wikipedia and similar Websites do not qualify as quality resources.
|
Which prevention strategy do you personally believe
: Which prevention strategy do you personally believe would be the most effective, and why? Which prevention strategy do you believe would be the least effective, and why
|
|
What is the projects net present value
: Empire Industries is considering adding a new product to their lineup. This product is expected to generate sales for four years after which time the product will be discontinued. What is the project's net present value if the firm wants to earn a 13..
|
|
Address enivromental health issues about e-waste disposal
: In particular , you discussed accontablility.As you noted the responsibility lies with the general public, manufacturing companies, and the government to address enivromental health issues such as E-waste disposal.What ideas do you have that would..
|
|
Economic growth for the typical firm
: Using the Internet, library, or other resources, research and briefly explain 2-3 methods currently being used to encourage economic growth for the typical firm in Hong Kong and for the typical firm in Singapore.
|
|
Examine risk assessment methodology is quantitative
: Examine whether your risk assessment methodology is quantitative, qualitative, or a combination of these, and discuss the main reasons why you believe that the methodology that you utilized was the most appropriate.
|
|
Write a paper that compare gaia hypothesis and avatar movie
: Write a paper that compare gaia hypothesis and avatar movie.
|
|
Required return on an index fund
: Bradford Manufacturing Company has a beta of 1.2, while Farley Industries has a beta of 0.3. The required return on an index fund that holds the entire stock market is 11.5%. The risk-free rate of interest is 6.75%. By how much does Bradford's requir..
|
|
Portfolio of assets displayed and compare
: On the Balance Sheet a user may look at Retained Earnings along with the portfolio of assets displayed and compare that to the liability side of the Balance Sheet.
|
|
Analyze economic-political environment in budget development
: Prepare an APA written paper that includes citations from professional literature relating to Higher Education. Analyze the budget processes of private and public colleges/universities. Analyze the economic/political environment in which budget devel..
|