Reference no: EM132333974
Assignment -
Part I. Research Question
Discuss a data routing protocol scheme that can be used in IoT networks. Your answer must clarify the following: (a) type of the routing service (link state or distance vector and connection-oriented or connectionless), (b) the technique adopted for discovering the paths; and (c) how to make path advertisement and maintenance and recovery [you may mention the scheme operations complexity].
Part II. Solve the following Questions
1. Suppose you are interested in detecting the number of hosts behind a NAT. You observe that the IP layer stamps an identification number sequentially on each IP packet. The identification number of the first IP packet generated by a host is a random number, and the identification numbers of the subsequent IP packets are sequentially assigned. Assume all IP packets generated by hosts behind the NAT are sent to the outside world.
a. Based on this observation, and assuming you can sniff all packets sent by the NAT to the outside, can you outline a simple technique that detects the number of unique hosts behind a NAT? Justify your answer.
b. If the identification numbers are not sequentially assigned but randomly assigned, would your technique work? Justify your answer.
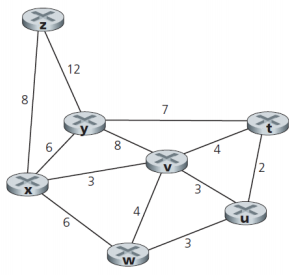
2. Consider the following network. With the indicated link costs, use Dijkstra's shortest-path algorithm to compute the shortest path from x to all network nodes. Show how the algorithm works by computing a table similar to the table shown in the lecture.