Reference no: EM131420808
Assignment: Intrusion Detection and Intrusion Prevention
Part 1: True or False Questions. Provide one or two sentences justification/explanation. Without justification you will not get full points.
1. T F Anomaly-based intrusion detection systems generate alerts based on deviations from "normal" traffic.
2. T F A host-based IDS only monitors network traffic destined for a particular computer.
3. T F When discussing IDS and IPS, a signature is a digital certificate used to identify the author of a rule.
4. T F To comply with network communication standards, software running on Internet hosts must implement both IP and ICMP protocols.
5. T F Signature-based intrusion detection can identify previously unknown attacks. Answer: _____
6. T F The primary difference between network-based IDS and IPS is that an IPS responds to suspected attacks by blocking network traffic, while an IDS only provides notification that suspicious traffic is observed.
7. T F Snort requires the use of at least one preprocessor to be able to analyze patterns in network traffic spanning multiple packets.
8. T F Snort generates an alert as soon as a detection rule is matched.
9. T F A network-based IDS that scans packet traffic to try to match known attack patterns is called a signature-based NIDS.
10. T F An in-line IDS must have the processing power to handle traffic at least as fast as the bandwidth of the network it monitors, or it will lose packets and potentially fail to notify on packets matching alert rules.
Part 2: Multiple Choice Questions. Print the correct answer in the blank following the question. With justification for the correct answer or reasons for others being not correct.
1. Which of the following is an advantage of anomaly-based detection?
a. Rules are easy to define
b. The data it produces can be easily analyzed
c. It can detect "zero-day" or previously unknown attacks
d. Malicious activity that falls within normal usage patterns is detected
e. Rules developed at one site can be shared with many other users
2. Most commercial IDSes generate alerts based on signatures at the network layer and what other OSI model layer?
a. Application layer
b. Presentation layer
c. Data-link layer
d. Transport layer
e. Session layer
3. Potentially troubling causes for network traffic with out-of-order packet arrival include all of the following EXCEPT?
a. The network route for inbound packets is different than the outbound route
b. The packets were routed through a network that uses small packet size
c. The packets have been altered in transit before arriving
d. The packets sent from the source were split across multiple interfaces
e. None of the above
4. Which is/are true for intrusion protection systems (IPSes)?
a. An IPS detects network attacks and issues alerts
b. An IPS responds to network attacks by blocking traffic and resetting connections
c. An IPS sits inline and monitors traffic
d. a and b only
e. a, b, and c
5. Which of the following is a limitation of Snort?
a. Cannot centrally monitor sensors running on different OSes
b. Cannot protect against insider threats
c. Cannot inspect encrypted traffic for attack signatures
d. Cannot scale effectively to protect a large network
e. All of the above
Part 3: Short Answers. Please answer briefly and completely, and cite all sources of information.
1. Compare and contrast signature-based and anomaly-based intrusion detection systems. In your analysis, describe at least three ways in which the two types of IDS are similar, and at least three ways in which they differ.
2. Identify and briefly describe the two primary approaches to writing signatures for network-based IDS tools. Is one technique preferred over the other? Explain why.
3. Describe what a pre-processor does in a network-based IDS tool such as Snort. Demonstrate your understanding of this functionality by citing two examples of pre-processors and explaining what they contribute to the process of network traffic analysis and intrusion detection.
4. If an attacker knew a network-based IDS was running in a targeted environment, how might the attacker try to evade detection? Provide at least two examples of IDS evasion techniques that might be used by an attacker, and suggest a remedy or defense against the techniques you cite.
5. Describe how host-based intrusion detection works, briefly contrasting it with network-based intrusion detection. Explain three types of threats against which HIDS is particularly effective.
Part 4: IDS Placement. (20 points) Please refer to the accompanying network diagram as you consider and respond to the following:
Global Corporation, Inc. (GCI) is a fictional company providing business services to a variety of clients across many industries, including commercial and government entities. GCI recently finished construction of a new corporate headquarters, which includes the network infrastructure for primary company operations. You are a security analyst specializing in intrusion detection brought in by GCI to help determine the most appropriate kinds of IDS to use and most effective IDS placements to protect their network.
GCI's network uses a conventional three-zone architecture: devices exposed to the Internet are part of an un-trusted outer zone; Internet-accessible services such as the company website and email are in a demilitarized zone; and major systems and servers supporting both Internet-facing and internal applications as well as internal computing resources such as the corporate LAN are in a trusted zone. Each of these zones is segmented from the others using hardware-based firewalls; the corporate databases are further protected behind their own dedicated firewall. GCI allows employees remote access to the corporate LAN using either VPN or dial-up connections.
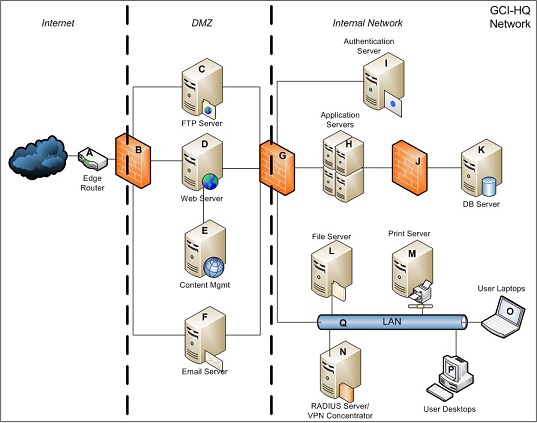
Identify the locations throughout the GCI network where you would recommend IDS to be deployed. Each of the components in the accompanying GCI-HQ Network diagram is lettered to simplify your references to the diagram. For network connections between devices and layers, you may assume for the purposes of this exercise that all components in a given zone share the same network segment. For each placement, you recommend, please note the type of IDS to be deployed and any specific considerations that should be taken into account to ensure the effective monitoring of the location.