Reference no: EM132475589
Section A: MULTIPLE CHOICE
Directions: Choose the correct answer by highlighting it with green.
Question 1. Which one of the flowing protocol is not a Network Management Protocol?
A. SNMP
B. CMIS
C. WEBM
D. CMIP
Question 2. Which Network Management model deals with the Network Management components and its relationship?
A. Organization Model
B. Information Model
C. Communication Model
D. Functional Model
Question 3. Identify an attack that can prevent or inhibits the normal use or management of communication facilities?
A. Modification
B. Denial of Service
C. Masquerade
D. Replay
Section 2: ESSAY
Directions: Answer the following items. Write your answer under each question.
Question 1. Mr. Anton prepared a message to send it to Ms. Charito, but is worried about the security. Identify and describe the confidentiality methods to provide security to his message.
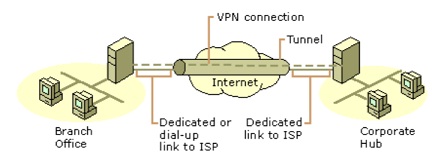
Question 2. Are the main office and the branch office as shown in the illustration below secured? Justify your answer.