Reference no: EM131516264
Question: Syslog
Earlier in this chapter, you viewed and manipulated log file entries on a computer running Windows. In this project, you do the same on a computer running the Linux operating system. Because Linux versions vary in the type of GUI application that allows you to open the system log, this exercise uses the command-line method instead. For this exercise, you need a computer with a Linux operating system installed, such as the Ubuntu Desktop VM that you created in Chapter 2. It need not be connected to a network, but for best results, it should be a computer that has been used in the past and not a fresh install. You must be logged on to the Linux computer as a user with administrator privileges.
1. If you are not already at a command-line (or shell) prompt, open a terminal session now.
2. The syslog file contains information similar to that shown in Figure 9-24. The first step in viewing your Linux computer's system log is to find out where the file is located. Try each of these commands until you find the syslog file that contains information similar to that in Figure 9-24
more /etc/syslog.conf
more/etc/rsyslog.conf
more/etc/rsyslog.d/50-default.conf
3. The first part of the syslog file appears. In this part of the file, you should see a list of log types and their locations, similar to the listing shown in Figure 9-24. (If you don't see the listing in this part of the file, press the Enter key until you do see it.)
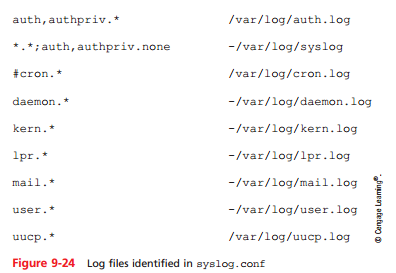
4. Write down the location and filename of the file that logs all events, as indicated by *.* in the first column. (For example, it might be /var/log/syslog or /var/adm/ messages.)
5. Press the Spacebar enough times to view the entire log configuration file and return to the command prompt.
6. Now that you know the name and location of your system log, you can view its messages. At the command prompt, type tail /var/log/syslog if your log file is at / var/log/syslog; if your log file is at /var/adm/messages, type tail /var/ adm/messages. Then press Enter.
7. The last 10 lines of your log file appear (assuming it is at least 10 lines long). What types of messages are recorded? When did the events occur?
8. Next you'll find out all the types of log files your computer saves. Type cd /var/log if your log file is in the /var/log directory, or type cd /var/adm if your log file is in the /var/adm directory. Then press Enter. You have changed your working directory to the same directory where log files are kept.
9. To view a listing of the directory's contents, type ls -la and press Enter. Notice the types of log files that appear in this directory.
10. Suppose you want to find every message in the system log file that pertains to DHCP addressing. At the command prompt, type grep DHCP syslog if your log file is named syslog or grep DHCP messages if your log file is named messages. Then press Enter. A list of messages containing the term DHCP appears. Consider how you might use grep and other UNIX commands in a script that would notify you each time a workstation on your network failed to obtain a DHCP-assigned IP address. (Note that this can be accomplished from most GUI system log interfaces, too.)
11. If your operating system is configured to start a new log file each day or each time the computer is restarted, your log file might be brief. Repeat Step 9 and, this time, look for other versions of the syslog or messages file in your working directory. For example, Ubuntu Linux will save older system messages in a file called syslog.0. If you find a larger, older log file, repeat Step 10 using this log file's name. How do the results differ?
12. Close the Linux terminal session window.