Reference no: EM13780248
Assignment On Mister Network Engineer
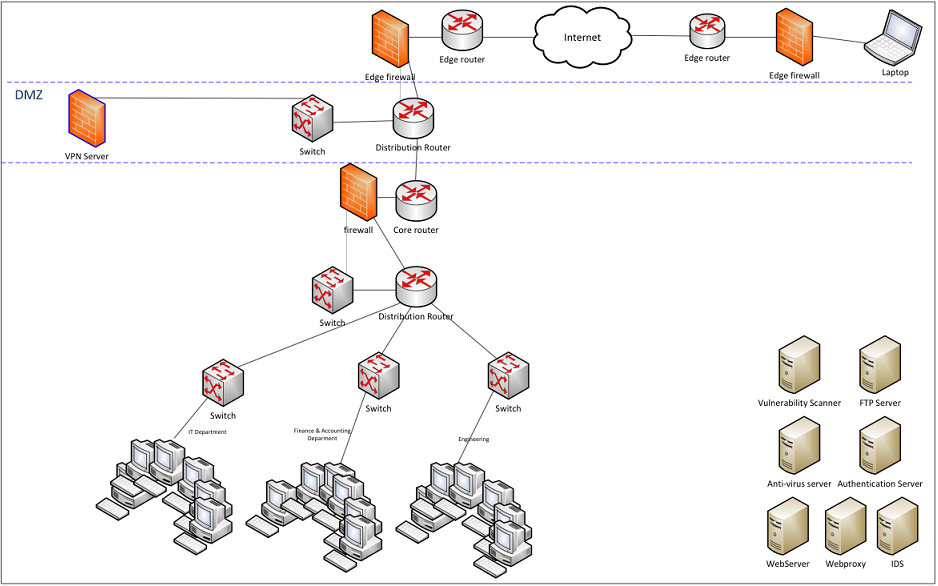
Using the network diagram below, your task is to incorporate the devices on the lower right into the diagram to create a secure corporate network. The devices you need to incorporate into the network diagram include: Web server, ftp server, vulnerability scanner, anti-virus server (client-based / server-based), Web proxy, intrusion detection system (IDS), and authentication server.
Note: All client-based / server-based devices work where a client is installed on a workstation, which has bidirectional communication with a corresponding server.
Write a four to five (4-5) page paper in which you:
1. Determine which devices you will use for both the current network diagram infrastructure consisting of firewalls, routers, and workstations as well as the device you need to incorporate. Include the following for each:
1. Make or vendor's name (e.g., Microsoft, Redhat, Cisco, Juniper, Netgear, 3Com, etc.)
2. Model (e.g., Windows 7, ASA 5500, Cisco 3500, Squid, etc.)
3. IP address assigned to all devices
2. Establish the configuration for each device in which you:
1. Research each of the devices you chose and provide a basic configuration you would use in your network.
2. Use IP addresses to describe your configuration.
3. Explain the impact that each of your configurations has on the security of the entire network.
4. Highlight at least five (5) security features for each device, including devices in network diagram.
3. Using Microsoft Visio or its open source alternative to create a final network diagram that incorporates all devices into the existing network and ensures the following:
1. VPN sessions (from laptop) are only allowed to access the desktops in the IT department by IT department employees.
2. All VPN connections from the Internet cloud into the corporate network terminate at the VPN server.
3. Users from Engineering and Finance and Accounting CANNOT communicate.
4. Vulnerability scans occur daily in which all desktops are scanned at least once per day.
4. Use at least three (3) quality resources in this assignment. Note: Wikipedia and similar Websites do not qualify as quality resources.
Your assignment must follow these formatting requirements:
· Be typed, double spaced, using Times New Roman font (size 12), with one-inch margins on all sides; citations and references must follow APA or school-specific format. Check with your professor for any additional instructions.
· Include a cover page containing the title of the assignment, the student's name, the professor's name, the course title, and the date. The cover page and the reference page are not included in the required assignment page length.
· Include charts or diagrams created in Visio or an equivalent such as Dia. The completed diagrams / charts must be imported into the Word document before the paper is submitted.
The specific course learning outcomes associated with this assignment are:
· Design a secure network to address a business problem.
· Use technology and information resources to research issues in network security design.
· Write clearly and concisely about Advanced Network Security Design topics using proper writing mechanics and technical style conventions.