Q. Show example on Hedge Fund?
Hedge Fund have been playing a no-lose game
In the easiest strategy a hedge fund borrows Hong Kong dollars (HKD) and then sells them in the market against USD that is they short the HKD. Note that this will results the money supply to shrink. A reduce in money supply leads to an interest rates increase. Raise in interest rates have several effects on the stock market. First borrowing HKD to purchase stocks becomes more expensive.
Therefore fewer investors would use margin. Second a raise in deposit interest rates will draw funds from stocks to deposits. Third interest rate raise are negative for businesses and their value will go down. Yet again stocks decline.
Alternatively higher interest rates lure more investors to park their money in Hong Kong boosting the currency. But they as well slam the stock market because rising rates hurt company's ability to borrow and expand.
However several of these Hedge Funds involved in the speculation didn't operate in the cash market. In its place they shorted the HKD in the futures markets. This doesn't require borrowing HKD. It is the counterparty who has to hedge the long HKD position that requires to borrow HKD from the banking system.
In the particular situation discussed here Hedge Fund managers believed that they were taking little risk
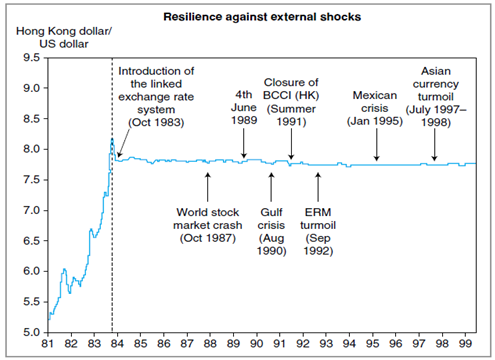
• The hedge funds stake on the collapse of the peg. If the dowel breaks the HKD is expected to fall. Specified the psychology of those days the casual view was that the HKD was overvalued. The merely risk to Hedge Funds is that the peg holds.
Under these conditions their loss will be the dissimilarity between the initial cost of entering the trade to sell HKD in futures markets and the pegged rate. The reading proposed that this cost is low.