PTR : Pointer:-
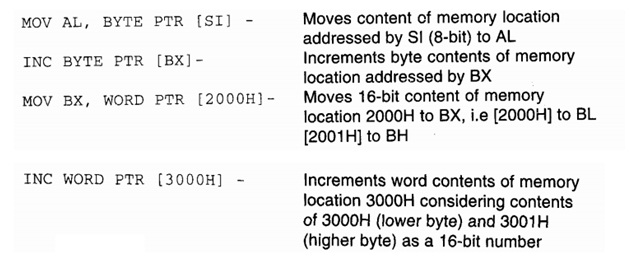
The pointer operator which is used to declare the type of a variable, label or memory operand. The operator PTR is prefixed by either WORD or BYTE. If the prefix is BYTE, then thespecific label, variable or memory operand is treated as an 8-bit quantity, whereas if WORD is the prefix, then it is treated as a 16-bit quantity. In other terms, the PTR operator is used to mention the data type - byte or word. The examples of the PTR operator are following:
Example :
In particular case of JMP instructions, the PTR operator is used to mention the type of the jump, for example near or far, as describe in the examples given below.
JMP WORD PTR [BX]-NEAR Jump
JMP WORD PTR [BX]-FAR Jump
PUBLIC As already described, the PUBLIC directive which is used along with the EXTRN directive. This give information to the assembler that the variables, labels, constants, or procedures declared PUBLIC can be accessed by other assembly modules to form their codes, but when using the PUBLIC declared variables, labels ,constants or procedures the user ought to declare them externals by using the EXTRN directive. Instead, the data types declared EXTRN in a module of the program, can be declared PUBLIC in at least any one of the other modules of the similar program. (Refer to the explanation on EXTRN directive to get the clear idea of PUBLIC.)