Reference no: EM131032710
Technology Review #2: Emerging Application of Technology in a Critical Infrastructure
This paper is the second of two Technology Reviews that you will research and write for this course. For this paper, you must choose an emerging application of technology which is suitable for future use in systems, hardware, or software which are used to operateor support a critical infrastructure.
The technology review papers will be used to prepare your technology selection paper for the Analysis of Alternatives exercise later in the course. Your audience for these papers is a group of senior executives who will be meeting to decide which emerging technologies or emerging applications of infrastructure technologies should be selected for one or more security-focused, Internal Research & Development projects during the next budget cycle. Each of these executives is responsible for a business area that will (a) develop systems and services which incorporate the emerging technologies or (b) depend upon such systems and services to support their organization's operation of portions of the identified critical infrastructure.
For this paper, you will perform the first three stages of the technology scan:
Technology scanning is an evaluation model that is used when you need to develop a list of candidate technology solutions. A technology scan can also be used when you need to obtain information about the latest advancements in security products and technologies.
SCOPING
The scoping phase of this technology scan has already been performed. For this paper, your scope is late stage1 and stages 2 through 5 (as shown in the figure below).
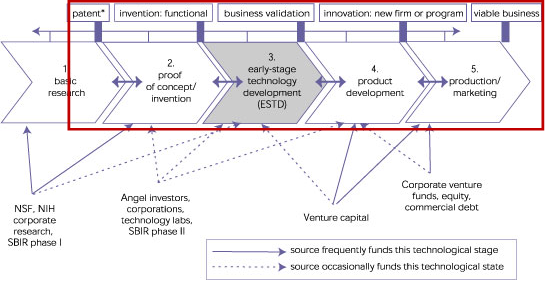
Image Source: https://www.atp.nist.gov/eao/gcr02-841/chapt2.htm
Your scope is further restricted to technologies which are used in the computers, digital devices, and other electronic / electrical technologies (this includes networks and network infrastructures) which will be deployed or used in a critical infrastructure. For definitions of critical infrastructures, seehttps://www.dhs.gov/critical-infrastructure-sectors
SEARCHING
To begin, select a technology which is in the basic research or proof of concept / invention (stage 1 and early stage 2 in the diagram above) and which meets the scoping restriction. You may use news articles, press releases, and government or company Web sites to help you find an appropriate technology. (Remember to cite these sources in your paper.)
Suggested technologies include:
• Autonomous Vehicles (ground, sea, or air): Transportation Systems Sector
• Crypto Currencies: Financial Services Sector (DO NOT CHOOSE Bitcoins)
• Deep Space Communication Networks: Communications Sector
• Implantable Medical Devices: Healthcare and Public Health Sector
• Precision Agriculture (integrated systems using satellite imagery, GPS, Sensors, Robots): Food & Agriculture Sector
• Robot inspectors for physical infrastructures (buildings, roads, railways, pipelines, etc.): Multiple Sectors
• Smart Grid (also called Advanced Metering Infrastructure): Energy Sector (DO NOT CHOOSE Smart Meters)
• Wearable Sensors for Hazardous Materials Detection (e.g. CBRNE): Emergency Services Sector
You are encouraged to look for and investigate additional appropriate technologies before deciding upon your technology choice for this assignment.
If you decide to research a technology that is not on the suggested technologies list (see above), you must first request and receive your instructor's permission. Your instructor may require that you do preliminary library searches for research papers and technical papers to prove that you can find a sufficient number of resources to complete the assignment.
Survey of the Professional Literature
During your survey of the professional literature, you will identify 10 research papers or technical papers which provide technical information about your selected technology (see selection requirements for each paper). These papers must be dated 2011, 2012, 2013, 2014, or 2015 (five year window).
Allowable sources for research papers / technical papers are: (a) professional journals, (b) conference proceedings, (c) dissertations or theses, and (d) technical magazines (published by either the ACM or IEEE). If an article from one of the above sources does not have a reference list containing at least 3 references you may use it in your review paper but it WILL NOT COUNT towards the "10 research or technical papers" requirement.
The requirement to "survey the professional literature" must be met by using research papers/publications and technical papers which are available from the following UMUC online library databases: ACM Digital Library, Dissertations & Theses (Pro Quest), IEEE Computer Society Digital Library, and Science Direct.
EVALUATING
In this stage, you will evaluate and report upon the information found during your survey of the professional literature. Read the abstract, introduction section, and closing sections for each of the sources identified in your survey of the professional literature. From this information, develop a summary of the technology that includes: (a) a description of technology and (b) planned uses of the technology (products, services, etc.). IMPORTANT: your technology review must incorporate information from each of your 10 "papers" from the professional literature.
Note: You may use other sources in addition to the papers which comprise your survey of the professional literature.
Next, brainstorm the security implications of this technology (if these are not specifically discussed by your sources). You should consider use of the technology to improve cybersecurity and uses which will negatively impact the security posture of an organization or the security of individual consumers or users of the product. It is very important that you consider BOTH SIDES OF THIS ISSUE.
Note: Remember that the security posture of a system or product is framed in terms of risk, threats, vulnerabilities, etc. Improvements to the security posture (positive security implications) will result in reduced risk, increased resistance to threats or attacks, and decreased vulnerability. Negative impacts on the security posture will result in increased risk, decreased resistance to threats / attacks, and increased vulnerability (weakness).
Write down your thoughts and ideas about the security implications of this technology using (a) the Five Pillars of Information Assurance and/or(b) the Five Pillars of Information Security.For your paper, you do not need to include all ten "pillars" but you should address a minimum of three. If you are targeting an "A" on your paper, address at least five of the pillars. (See Technology Review #1 Detailed Project Description for definitions of the pillars and references.)
You should provide specific examples using characteristics and/or applications of the technology, e.g. an emerging nanotechnology which can be used to tag "genuine" parts with an identification code. Such a technology may be chosen to replace etched serial numbers or bar codes because the new tags will decrease the probability that substitute or non-genuine parts will enter the supply chain undetected. This will, in turn, decrease the risk of substitution which then decreases the probability of loss of availability caused by non-genuine parts. Decreasing the probability of a negative event will decrease the risk associated with that event.
WRITING YOUR EVALUATION
Your paper must provide the reader with an overview of the technology followed by information about the potential security risks and/or benefits of its use(the security posture).You MUST use information paraphrased from the papers found during your Survey of the Professional Literature (with appropriate in-text citations).
The Technology Review papers must be at least 3 pages in length but no more than 5 pages (excluding the title page and references page).
The papers should comply with the formatting guidance given by your instructor. All papers in this course must also comply with APA Style for references and citations.