Q. Explain XLAT instruction with help of example?
Let's presume a table of hexadecimal characters signifying all 16 hexadecimal digits in table:
HEXA DB '0123456789ABCDEF'
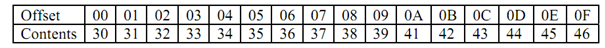
The table comprises the ASCII code of every hexadecimal digit:
(All value in hexadecimal)
If we place 0Ah in AL with the thought of converting it to ASCII we have to set BX to offset of HEXA and invoke XLAT. You need not specify table name with XLAT hence it is implicitly passed by setting BX to HEXA table offset. This instruction would do the subsequent operations:
It will first add AL to BX producing an effective address which points to eleventh entry in the HEXA table.
Content of this entry is now moved to AL register which means 41h is moved to AL.
Or we can say in other words, XLAT sets AL to 41h since this value is located at HEXA table offset 0Ah. Please consider that 41h is the ASCII code for hex digit A. The subsequent sequence of instructions will accomplish this:
MOV AL, 0Ah ; index value
MOV BX, OFFSET HEXA; offset of the table HEXA
XLAT
The above tasks can be executed without XLAT instruction however it will need a long series of instructions like:
MOV AL, 0Ah ; index value
MOV BX, OFFSET HEXA ; offset of the table HEXA
PUSH BX ; save the offset
ADD BL, AL ; add index value to table
; HEXA offset
MOV AL, [BX] ; retrieve the entry
POP BX ; restore BX