Hyper Cube: A Hypercube interconnection network is an expansion of cube network. For n=3, Hypercube interconnection network may be described recursively in this manner:
For n = 3, it cube network in that nodes are allocated number 0, 1, ......,7 in binary. In different way, one of the nodes is allocated a label 000, another one as 001.... and the final node as 111. Then whichever node can communicate with another node if their labels vary in accurately one place, for example the node with label 101 can communicate straight with 001, 000 and 111.
For n > 3, a hypercube may be described recursively in this manner:
Take two hyper cubes of dimension (n - 1) every having (n -1) bits labels as 00....0, ......11.....1
Next link the two nodes having similar labels each (n - 1) dimension hypercubes and link these nodes. Next prefix "1" the labels of one of the (n - 1) dimensional hypercube and "0" to labels of other hypercube. This entirely completes the structure of n-dimensional hypercube. Straight/Direct connection is just between that pair of nodes that has a (solid) line associating the two nodes in pair.
For n = 4 we draw 4-dimensional hypercube as displayed in Figure:
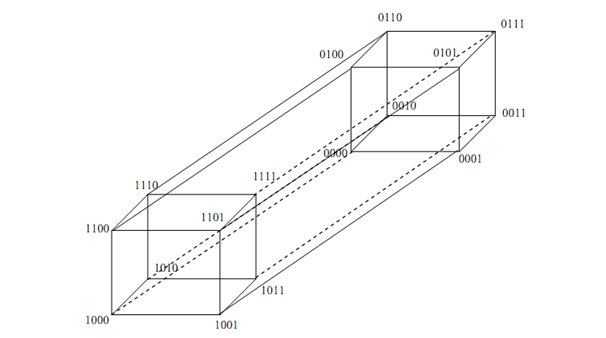
Figure: 4-Dimensional hypercube