Reference no: EM132377635
Assignment: Firewalls
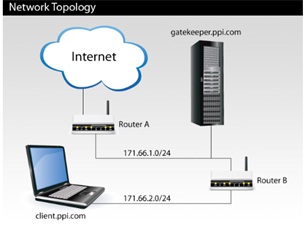
Your company, Plush Packet, Inc., has the following network topology:
Plush Packet is worried that a Trojan virus infecting one of its internal machines may steal proprietary source code and send it outside the internal network. Therefore, every employee is issued a small hardware authentication device. Any communication to the outside world must be authenticated by a human typing in a security code computed by and displayed on this device. To enforce the policy, the administrators set up a single machine, gatekeeper.ppi.com, that manages interactions between internal company machines and the rest of the Internet.
Employees can log into gatekeeper from internal machines using SSH and their hardware authentication device. From gatekeeper, they can SSH to the rest of the Internet. Internal machines are on a separate subnet (171.66.2.0/24) and can exchange packets with gatekeeper but not with the outside world. Machines on the outside Internet are not able to SSH to gatekeeper.
Question 1. Describe how to enforce this policy with simple (or stateless) packet filtering on Router A and/or Router B. Describe the precise packet filtering rules you would put in place at each router.
Question 2. After several days of this new policy, employees become annoyed that many applications seem to lock up for periods of a minute or so. IT suspects that the problem is caused by attempts to create TCP connections to the outside world, which, instead of failing instantly, take approximately 1 minute. After all, clients' TCP implementations treat packets dropped by the firewall policy just the same as packets dropped because of congestion-they back off and keep trying. To solve the problem, the administrators reconfigure their routers not just to drop packets silently, but in certain cases to send packets back to the source of a dropped packet. Describe precisely what the routers can send back to make prohibited outgoing TCP connections fail quickly. (Assume they cannot make any changes to the TCP implementation on clients.)
Remember to properly cite your sources according to APA guidelines.