<TEXTAREA> specifies a form field where user can enter large amounts of text. In most respects, <TEXTAREA> works like an <INPUT> field. It can have a name as well as a default value. It has to be concerned that <TEXTAREA> is a container tag, so it has a start tag as well as an ending tag.
In its simplest form, <TEXTAREA> requires NAME, COLS and ROWS attributes and nothing between <TEXTAREA ...> and </TEXTAREA>. Look at the code fragment demonstrated below
<FORM ACTION="../cgi-bin/mycgi.pl" METHOD=POST>
your comments:<BR>
<TEXTAREA NAME="comments" COLS=40 ROWS=6></TEXTAREA>
<P><INPUT TYPE=SUBMIT VALUE="submit">
</FORM>
Gives us this form...
your comments:
Matter between <TEXTAREA ...> and </TEXTAREA> are used as the default value
<FORM ACTION="../cgi-bin/mycgi.pl">
your response:<BR>
<TEXTAREA NAME="comments" COLS=40 ROWS=6>
Kamal said
: I think it's a great idea
: but it needs more thought
</TEXTAREA>
<P><INPUT TYPE=SUBMIT VALUE="submit">
</FORM>
gives us your response:
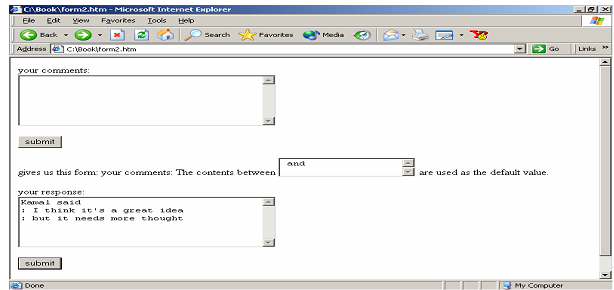
Figure: Using the TEXTAREA Tag
Contents are interpreted as text only; HTML markup is ignored. Theoretically user can type unlimited amounts of text into textarea field. In practice browser sets a limit which is usually no more than 32 K. If you want users to send in their latest novel, consider using some file upload mechanism.