Give the organization of centralized store program control (SPC).
Within stored program control systems, a program or set of instructions for the computer that is stored in its memory and the instructions are executed automatically separately by the processor. Carrying out the exchange control functions by programs stored into the memory of a computer led to such name.
Now here are two approaches to organizing stored program control:
1. Centralized: in such type of control, all the control equipment is replaced through a single processor that must be fairly powerful.
2. Distributed: in this type of control, the control functions are shared through several processors inside the exchange itself.
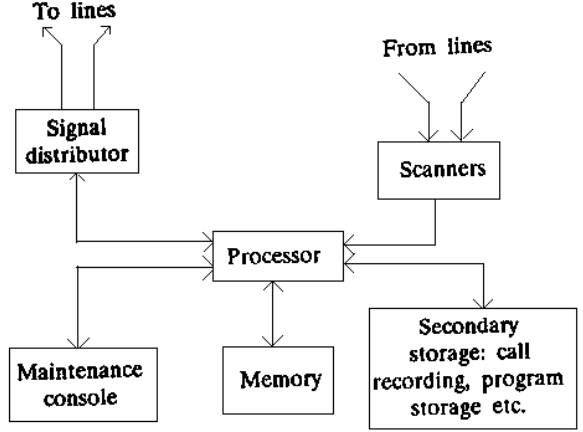
FIG - classically Centralized SPC Organization
Dual processor architecture may be configured to operate into one of three modes, in centralized SPC:
1. Standby mode: In such mode, one processor is active and another is on standby, both software and hardware wise. The standby processor brought online while active processor fails. A significant requirement of this configuration is the capability of the standby processor to reconstitute the state of the exchange system while this takes over the control.
2. Synchronous duplex mode: In this synchronous duplex mode, hardware coupling is given in between the two processors that execute similar set of instructions and compare the results continuously. The faculty processor is identified and taken out of service instantly, if a mismatch occurs. While the system is operating usually, the two processors have similar data in their memories at all the times and receive all the information from the exchange environment.
3. Load Sharing mode; in this load sharing operation, an incoming call is allocated randomly or into a predetermined order to one of the processors that then handles the call right by completion. Therefore both the processors are active concurrently and share the load and the resources dynamically.