Concept Of Permutation Network
In permutation interconnection networks the information transfer necessitates data transfer from input set of nodes to output set of nodes and potential connections between edges are set up by implementing several permutations in accessible links. There are several networks where multiple paths ranging from source to destination are probable. For discovering the possible routes in these networks study of the permutation concept is a necessity.
Let us look at the basic concepts of permutation with respect to interconnection network. Let us say the network has set of n input nodes and n output nodes.
Permutation P for a network of 5 nodes (i.e., n = 5) is written like this:
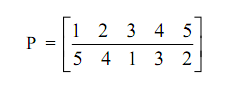
It signifies node connections are 1↔5, 2↔4, 3↔1, 4↔3, 5↔2.
The connections are displayed in the Figure below.
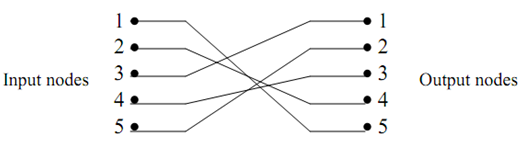
Figure: Node-Connections
The other permutation of the similar set of nodes can be
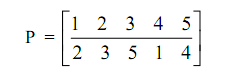
That means connections are: 1↔2, 2↔3, 3↔5, 4↔1, and 5↔4 similarly other permutations are also possible. The set of all permutations of a 3 node network would be