Q. Example to show directory in doc?
Like a file name, the directory name may also have up to eight alpha-numeric characters. The directory name can also have an extension name up to 3 characters long. However, the extension name is not used with the directory name.
When you start your PC, it generally responds with ‘C :/>' and selects the main or the root directory of drive C. Any file that you create or copy to drive C is added to this root directory. If you continue to add files in the root directory, few days after, the root directory will have too many files. This will not only puzzle you, it will also make the PC slow. If there are too many files in a directory the PC may take too long to find or open the files. You should try to use directories (and sub directories) in your hard disk
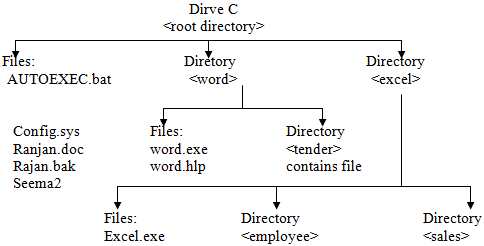
DOS always creates a root directory in each story device. You can create new directories in the root directory of the hard disk or floppy disk. You can keep files in these directories. Moreover, beside files, each directory can also have directories. Those, the file and directory organization in DOS looks like the roots of a tree. here, the root directory in drive C contains if you files in two directories - EXEL and WORD . The WORD directory contains some files as well as a directory TENDER. Sometimes, the second level directory (TENDER in this case) is termed as sub-directory. The root directory contains another directory - EXCEL. This directory contains a few files as well as two directories - SALES and EMPLOYEE. Both these directories contain files.
Structure can be created at any level of directory. For example, a new directory, say FOXPRO directory may contain files as well as more directories. If you want, you can takes out files from any directory or more files to another directory. You can also remove an enter directory.