Communications Programs : By communications programs, we mean those programs which allow a computer to communicate via a transmission cable to another electronic device. Here we do not include multi-user system or small networks. We are mainly interested in communications for rapid data input and retrieval, and so we consider the telephone network as the transmission medium. Computer communications are most easily explained in Figure.
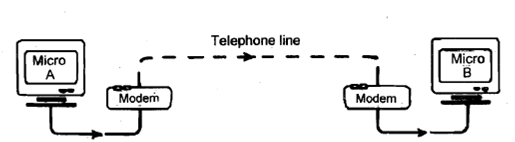
Figure: Computer Communications
This allows one personal computer 'talking' to another. PC A reads a data file, say, from its floppy disk and sends it to a modem (Modulator - Demodulator). Here, PC A's electronic signal (the data file) is converted into a signal that can be transmitted over a telephone line. B can only read PC A's signal by receiving the signal via its own modem which translates the signal back into a computer signal. In fact, this example is typical for most computer communications over telephone lines:
(I) Between mainframe computers, or
(2) Between PCs and mainframes.
This situation is illustrated in Figure and is the basis on which PC users can communicate with the outside world.
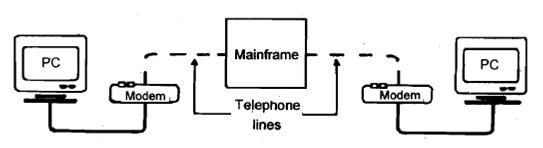
Figure: PC Mainframe Communicates
There are two main uses of PC to mainframe communications which may assist you in the management of your work. The first is accessing national databases and the second is electronic mail.
There are many databases for which you can become a subscriber and which your computer can access more or less at the touch of a button to obtain specialist information.