Reference no: EM13921017 , Length: 1225 Words
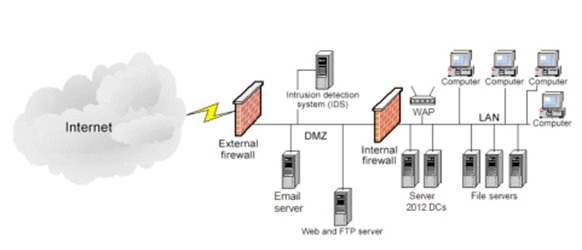
You have just been hired as an Information Security Engineer for a videogame development company. The organization network structure is identified in the below network diagram and specifically contains:
1) 2 – Firewalls
2) 1 – Web / FTP server
3) 1 – Microsoft Exchange Email server
4) 1 – Network Intrusion Detection System (NIDS)
5) 2 – Windows Server 2012 Active Directory Domain Controllers (DC)
6) 3 – File servers
7) 1 – Wireless access point (WAP)
8) 100 – Desktop / Laptop computers
9) VoIP telephone system
The CIO has seen reports of malicious activity being on the rise and has become extremely concerned with the protection of the intellectual property and highly sensitive data maintained by your organization. As one of your first tasks with the organization, the CIO requested you identify and draft a report identifying potential malicious attacks, threats, and vulnerabilities specific to your organization. Further, the CIO would like you to briefly explain each item and the potential impact it could have on the organization.
Write a four to five (4-5) page paper in which you:
1. Analyze three (3) specific potential malicious attacks and / or threats that could be carried out against the network and organization.
2. Explain in detail the potential impact of the three (3) selected malicious attacks.
3. Propose the security controls that you would consider implementing in order to protect against the selected potential malicious attacks.
4. Analyze three (3) potential concerns for data loss and data theft that may exist in the documented network.
5. Explicate the potential impact of the three (3) selected concerns for data loss and data theft.
6. Propose the security controls that you would consider implementing in order to protect against the selected concerns for data loss and data theft.
7. Use at least three (3) quality resources in this assignment (no more than 2-3 years old) from material outside the textbook. Note: Wikipedia and similar Websites do not qualify as quality resources.
Your assignment must follow these formatting requirements:
• Be typed, double spaced, using Times New Roman font (size 12), with one-inch margins on all sides; citations and references must follow APA or school-specific format. Check with your professor for any additional instructions.
• Include a cover page containing the title of the assignment, the student’s name, the professor’s name, the course title, and the date. The cover page and the reference page are not included in the required assignment page length.
The specific course learning outcomes associated with this assignment are:
• Explain the concepts of information systems security as applied to an IT infrastructure.
• Describe the principles of risk management, common response techniques, and issues related to recovery of IT systems.
• Describe how malicious attacks, threats, and vulnerabilities impact an IT infrastructure.
• Explain the means attackers use to compromise systems and networks, and defenses used by organizations.
• Use technology and information resources to research issues in information systems security.
• Write clearly and concisely about network security topics using proper writing mechanics and technical style conventions.
|
Who will supply the best materials at most reasonable price
: Perform marketing research with objective To find the best vendor who will supply the best materials at most reasonable price. Procurement report.
|
|
Behavioral economics discussions often start from the observ
: 1. Behavioral economics discussions often start from the observation that in many circumstances people are "consistently irrational". This implies that- 2. One of the reasons why physicians earn more money per hour than nurses is:
|
|
Teaching in the clinical setting
: In the assignment should have the case scenario like preceptor teach preceptee etc. (prefer in medical ICU settings). Should use some theories like Bandura social learning theory, learning style like Kolb's learning style inventory or VAT learning st..
|
|
Describe the relevance of the nursing research problem
: Describe the relevance of the nursing research problem addressed in a SRR to practice. (CO 3, 6). Critique the levels of evidence of the studies used in the SRR, specifically the designs of the studies included. (CO 6)
|
|
You have just been hired as an information security engineer
: You have just been hired as an Information Security Engineer for a videogame development company. The organization network structure is identified in the below network diagram and specifically contains:
|
|
Tell us about an entrepreneur who has inspired you
: What are the qualities that has made him successful and famous, Why does he inspire you and how can you implement his inspiration to use in your life.
|
|
How much pollution reduction
: Appalachian Coal Mining believes that it can increase labor productivity and, therefore, net revenue by reducing air pollution in its mines. It estimates that the marginal cost function for reducing pollution, How much pollution reduction should App..
|
|
What are costs of debt and preferred stock
: What are costs of debt, preferred stock, and equity components of capital? What is Cowboy's WACC
|
|
Calculate the total direct labor cost in department
: Calculate the total direct labor cost in Department A. Calculate the direct labor wage rate in Department B, 2. Compute the rate to be used in each department for applying overhead in both departments
|