Reference no: EM13683419
1. General Security Concepts
Identify which security requirement was violated in the following cases:
a. Eve peeks at Alice's password when she logs in.
b. Eve logs into Alice's account and stops the web server that was running.
c. There is a process running in Alice's machine, which is updating a database from a remote machine. Eve interrupts the process, resulting in inconsistent database.
2. Symmetric Encryption
Padding may not always be appropriate. For example, one might wish to store the encrypted data in the same memory buffer that originally contained the plaintext. In that case, the ciphertext must be the same length as the original plaintext. A mode for that purpose is the ciphertext stealing (CTS) mode. Figure (a) below shows an implementation of this mode.
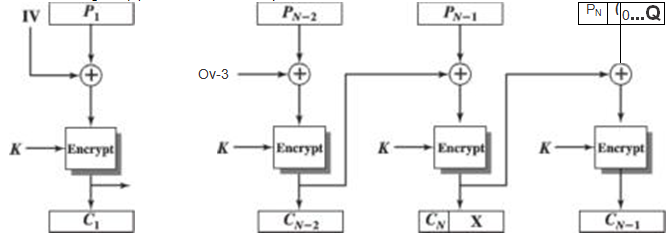
a. Explain how it works.
b. Describe how to decrypt Cn _i and Cn.
3. Public-Key Cryptography and Message Authentication
1. Suppose Bob uses the RSA cryptosystem with a very large modulus n for which the factorization cannot be found in a reasonable amount of time. Suppose Alice sends a message to Bob by representing each alphabetic character as an integer between 0 and 25 (A ^ 0, . . ., Z ^ 25), and then encrypting each number separately using RSA with large e and large n. Is this method secure? If not, describe the most efficient attack against this encryption method.
Consider the following PKI system: An arrow from A to B (A ^ B) means that A issued a certificate for B's public key. Assume further that everybody in the system trusts A and has A's certificate:
A SI *
B C
G
In order for B to send a confidential message to G, B must acquire G's public key. Assume anyone knows only its own public/private keys. What is the chain of certificates that B needs to acquire and verify?
4. Key Distribution and User Authentication
The following is a proposed mutual authentication protocol:
Alice
Hi, I'm Alice
Hash(KAiice.Bob, Random + 1)
What are the possible flaws in this protocol? Propose how to fix the possible flaws with minimal modifications to the protocol.
5. Transport-Level Security/IP Level Security
Make some recommendations about how you would implement transport-level security and/or IP level Security for the following use cases:
a. Your company has an e-commerce website that accepts credit card payments. Your clients could use any browser to access your website, and they might not have any prior relationship with your company. You want to make sure that they "feel" safe when they access your website. You do not want any third party to eavesdrop on the communications between your clients and your website, as they could steal credit card numbers from your clients. You do not want any third party to be able to modify, inject or replay any traffic during the session.
b. Your company has a back office servers that need to be accessed by mobile/remote employees through the Internet. Those servers are critical to the operation of your business: You do not want unauthorized users to be able to access the back office servers. You do not want any third party to eavesdrop on the communications to/from your back office servers. You do not want your remote employees to connect to a 'rogue' back office server. Finally, you want to be protected against injection and replay attacks.
For each use case, please indicate how you would configure the servers and the clients, i.e., how should SSL, SSH or IPSec be parameterized on you servers/clients (You do not need to provide the exact commands or directives, but you should give details, such as the protocols versions/types to be used, ...). Also indicate which key materials are needed and how they are distributed/acquired.