Reference no: EM13945231
P3. UDP and TCP use 1s complement for their checksums. Suppose you have the following three 8-bit bytes: 01010011, 01010100, 01110100. What is the 1s complement of the sum ofthese 8-bit bytes? (Note that although UDP and TCP use 16-bit words in computing the checksum, for this problem you are being asked to consider 8-bit sums.) Show all work. Why is it that UDP takes the 1s complement of the sum; that is, why not just use the sum? With the 1s complement scheme, how does the receiver detect errors? Is it possible that a 1-bit error will go undetected? How about a 2-bit error?
P4. a. Suppose you have the following 2 bytes: 01011100 and 01010110. What is the 1s complement of the sum of these 2 bytes?
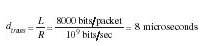
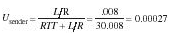
P14. Consider the cross-country example shown in Figure 3.17. How big would the window size have to be for the channel utilization to be greater than 95 percent? Suppose that the size of a packet is 1,500 bytes, including both header fields and data.
P19. Consider the GBN protocol with a sender window size of 3 and a sequence number range of 1,024. Suppose that at time t, the next in-order packet that the receiver is expecting has a sequence number of k. Assume that the medium does not reorder messages. Answer the following questions: a. What are the possible sets of sequence numbers inside the sender's window at time t? Justify your answer. b. What are all possible values of the ACK field in all possible messages currently propagating back to the sender at time t? Justify your answer.
P53. In this problem, we consider the delay introduced by the TCP slow-start phase. Consider a client and a Web server directly connected by one link of rate R. Suppose the client wants to retrieve an object whose size is exactly equal to 15 S, where S is the maximum segment size (MSS). Denote the round-trip time between client and server as RTT (assumed to be constant). Ignoring protocol headers, determine the time to retrieve the object (including TCP connection establishment) when
a. 4 S/R > S/R + RTT > 2S/R
b. S/R + RTT > 4 S/R
c. S/R >RTT
|
Visit the endeavour space shuttle
: Visit the Endeavour Space Shuttle (any day) at the Science Center. Fees vary so visit the Reservation Desk for info. For directions click here. It's near USC in downtown LA.
|
|
Comparative advantage in borrowing floating
: IRS Suppose Company X is an international company and its client is requesting a 10-year $5,000,000 floating-rate loan. Company Y needs $5,000,000 to finance a 10-year project. X is an AAA-rated bank and Y is a BBB-rated company. Based on their borro..
|
|
Topic of effective and ethical communication
: Design an algorithm and use it to write a Python program that reads the contents of the data file into a list. The program should then loop, to allow a user to check various numbers against those stored in the list.
|
|
What is a lower bound for the value of the futures option
: Consider a four-month futures put option with a strike price of 100 when the risk-free interest rate is 10% per annum. The current futures price is 87. What is a lower bound for the value of the futures option if it is (a) European and (b) American?
|
|
Udp and tcp use 1s complement for their checksums
: Suppose you have the following 2 bytes: 01011100 and 01010110. What is the 1s complement of the sum of these 2 bytes?
|
|
Trading costs and taxes
: You purchased six TJH call option contracts with a strike price of $40 when the option premium was quoted at $1.30. The option expires today when the value of TJ stock is $41.90. Ignoring trading costs and taxes, what is your total profit or loss on ..
|
|
Importance of standards in networking technology
: Question 1: Explain how antenna polarization can affect the reception of RF signals. Question 2: Discuss the importance of standards in networking technology and in communications in general. Evaluate how standards have helped to shape commonly us..
|
|
Discuss the different kinds of prophets
: Discuss the historical background during the time of the kingdoms of Israel and Judah. Your response does not have to be in depth, but please respond in 2 or 3 paragraphs.
|
|
Regard to payroll and accounts payable functions
: Sasha Company allocates the estimated $196,400 of its accounting departments costs to its production and sales departments since the accounting department supports the other two departments particularly with regard to payroll and accounts payable fun..
|