Reference no: EM13538
Recursive tree algorithms
Algorithms to Write:
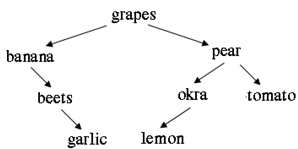
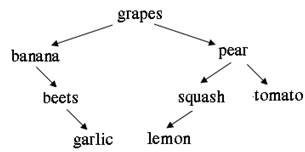
1. Write a recursive function to determine if a binary tree is a binary search tree. For example, in the trees above, the tree on the left is a binary search tree, while the tree on the right is not.
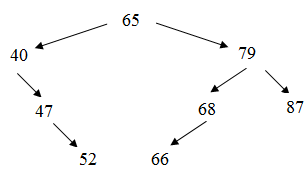
2. The location of a node in a binary search tree is defined as a string such as LLRRL, which represents the node that you find by starting at the root, and traversing Left, traverse Left, traverse Right, traverse Right, and traverse Left. Write a function to print a path to some target 'x' based on the direction from the root to the target. For example, in the tree above, the path from 65 to 52 is LRR. Hint: use a stack to store the path.
3. Write a recursive algorithm to count the number of right children in a binary search tree.
4. Write the method levelCount whose header is given below. Method levelCount returns the number of nodes on the specified level.
int BinarySearchTree<Type> :: levelCount(BinaryNode<Type>* t, int level);
For this problem, the root is at level zero, the root's children are at level one, and for any node N its level is one more than N's parent's level. For example, for the bean-tree diagrammed below, the call levelCount(t,1) should return 2 (chickpea and navy are on level 1); the call levelCount(t,2) should return 3; and the call levelCount(t,4) should return 0.
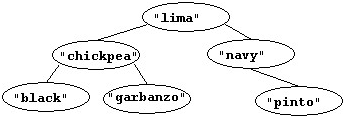
Hint: when the level is 0, there is always just one node at that level, the root node (assuming it isn't empty), so return 1. If the level isn't zero, recursive calls will be used to determine the number of nodes at the requested level, and the level-requested should change in the recursive calls.
5. Write a recursive algorithm to delete the leaves of a binary tree.
Programming Requirements
You must use the binary search tree code provided. Each algorithm must be implemented as both a private method and a public method of the class. Your code will be tested using the program provided.
Other Requirements
- File names must match exactly to the file names provided
- Clearly state any additional assumptions you may need to make.
|
Force of the water on the gate
: Determine the magnitude of the horizontal and vertical components of the force of the water on the gate.
|
|
Create a shopping cart in asp
: The users will use a browser to access the on-line store. The web server software for the production web server is Windows 2003 Server /IIS6.
|
|
Create a structural model
: Structural modeling is a different view of the same system that you analyzed from a functional perspective. This model shows how data is organized within the system.
|
|
Express the shannon-hartley capacity theorem
: Express the Shannon-Hartley capacity theorem in terms of where is the Energy/bit and is the psd of white noise.
|
|
Recursive tree algorithms
: Write a recursive function to determine if a binary tree is a binary search tree.
|
|
Develop a reliable transfer protocol over udp
: Develop a reliable transfer protocol over UDP. Focus on a Stop- and-Wait protocol.
|
|
Create a web site for an apple farm
: Create a web site for an apple farm. Create an HTML5 form allowing visitors to create an account with the site. Account details are to be stored in your MySQL database. Information should be stored in a secure way.
|
|
Stock market project
: Select five companies for the purpose of tracking the stock market, preparing research on the companies, and preparing company reports.
|
|
Shopping cart program for web applications class
: Shopping Cart program for web applications class. Allows user to browse while keeping track of the items in which they will purchase at the end on the order page link and this will give a final price for all items.
|