Reference no: EM132486421
CO4512 - Information Security Management - University of Central Lancashire
Assignment: Risk Assessment Report
Learning Outcome 1 - Select and use applicable standards and methods for information security and risk management.
Learning Outcome 2 - Conduct and properly document risk assessment based on a given scenario.
Learning Outcome 3 - Find and evaluate appropriate published information to remain up-to-date about threats, vulnerabilities and patches.
Scenario Description
UCLanRE is a new Real Estate agency in Preston, and its current IT infras- tructure is depicted in Figure 1. The IT infrastructure comprising:
(i) Office personal computers (PCs) running Windows XP for employees;
(ii) A machine running SQL server, which stores all information about customers and real estates;
(iii) A machine running a mail server and stores all emails and at- tached files.
(iv) A machine running an IIS web server hosting the website of UCLanRE on which users can browse for real estates, register themselves and contact the employees;
(v) All the servers and office PCs are connected to a net- work switch so that they can communicate with each other. The router serves as a gateway between the internal network and the internet.
(vi) Internet Information
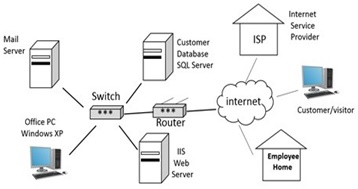
Figure 1: The IT infrastructure of UCLanRE.
Services (IIS, formerly Internet Information Server) is an extensible web server created by Microsoft.
After some attack incidents and financial loss, the agency realized that it should carry out a risk assessment and improve its IT infrastructure with security con- trols.
Your task
In this assignment you have to:
1. Conduct a risk assessment on the network in Figure 1, based on the ISO 27005 standard.
2. Write a detailed risk assessment report (see Section 4 for the required struc- ture).
Attachment:- Information Security Management.rar