Reference no: EM13945839
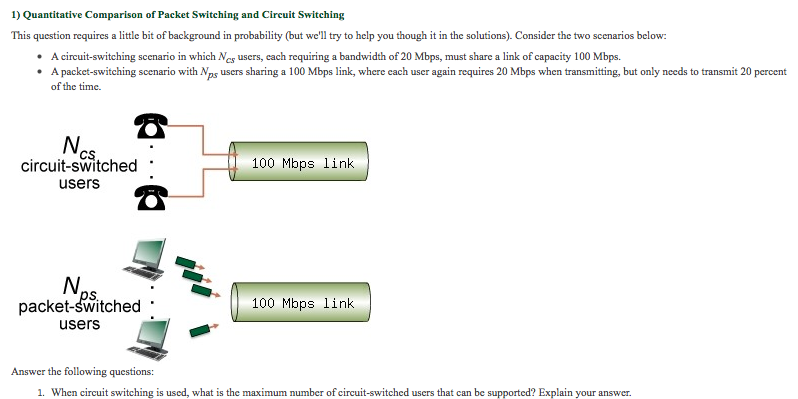
Consider the two scenarios below:
A circuit-switching scenario in which Ncs users, each requiring a bandwidth of 20 Mbps, must share a link of capacity 100 Mbps.
A packet-switching scenario with Nps users sharing a 100 Mbps link, where each user again requires 20 Mbps when transmitting, but only needs to transmit 20 percent of the time.
Answer the following questions:
a. When circuit switching is used, what is the maximum number of circuit-switched users that can be supported? Explain your answer.
For the remainder of this problem, suppose packet switching is used. Suppose there are 9 packet-switching users (i.e., Nps = 9).
b. Can this many users be supported under circuit-switching? Explain.
c. What is the probability that a given (specific) user is transmitting, and the remaining users are not transmitting?
d. What is the probability that one user (any one among the 9 users) is transmitting, and the remaining users are not transmitting? When one user is transmitting, what fraction of the link capacity will be used by this user?
e. What is the probability that any 5 users (of the total 9 users) are transmitting and the remaining users are not transmitting? (Hint: you will need to use the binomial distribution [1, 2]).
f. What is the probability that more than 5 users are transmitting? Comment on what this implies about the number of users supportable under circuit switching and packet switching.
|
Define wireless equipments
: The reason for putting together my own home network was for one the other desk top was in another room and I did not want to run a cord all over the home to the router.
|
|
Realistic example of a rational consumer motive
: Describe a real or made up but realistic example of a rational consumer motive that you or someone you know has experienced. What product did you buy, and what was your motive for buying it?
|
|
What resources or materials do you have on-hand
: Where are you? What is around you? What resources or materials do you have on-hand? What does it sound like? What does it feel like (temperature, etc.)? Are other people there? Do you sit at a desk, on the floor, in a beanbag chair
|
|
Does police culture encourage corruption
: We have all heard the saying "one bad apple spoils the whole bunch". • What is the "rotten apple" theory?
|
|
Can this many users be supported under circuit-switching
: A circuit-switching scenario in which Ncs users, each requiring a bandwidth of 20 Mbps, must share a link of capacity 100 Mbps.
|
|
What information does the company provide
: Look at the contents page. What information does the company provide? Find the financial highlights page. What are the items of accounting information which the company wants you to note?
|
|
What is the marginal transformation rate for each country
: What is the marginal transformation rate for each country? Should the two countries specialize and trade? If so, who has the comparative advantage in what product? Once they specialize, how much does output increase?
|
|
Prepare a paper about yourself
: Prepare a multi-page, paper about yourself. Discuss the issues listed below in short paragraph format. Include pictures when possible: Where were you born? Where is your family from? What is your culture? Where are you from
|
|
What are possible countermeasures
: What possible security problems arise if an adversary manages to alter the clock used by legitimate clients? What are appropriate countermeasures in this case?
|