Problems
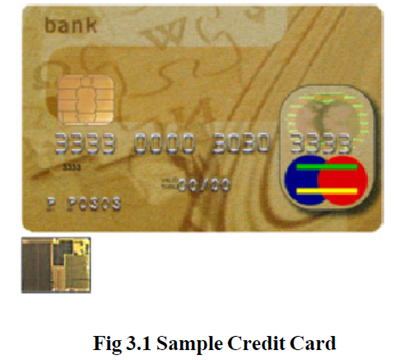
A smart card, join credit card and debit card properties. The 3 by 5 mm security chip surrounded in the card is exposed enlarged in the inset. The contact pads on the card permit electronic right of entry to the chip.
The low security of the credit card system presents countless breaks for fraud. This chance has formed a enormous black market in stolen credit card numbers, which are usually used quickly previous to the cards are reported stolen.
The objective of the credit card corporations is not to get rid of fraud, but to "reduce it to manageable levels". This involves that high-cost low-return fraud avoidance actions will not be used if their cost go beyond the possible get from fraud decrease. the majority internet fraud is done from side to side the use of stolen credit card information which is get in many ways, the easiest being copying information from retailers, either offline or online. Despite hard work to get better security for remote purchases using credit cards, systems with security holes are typically the result of poor implementations of card attainment by merchants. For instance, a website that uses SSL to encrypt card numbers from a client may just email the number from the web server to somebody who manually processes the card details at a card terminal. Obviously, wherever card details become human-readable before being processed at the acquiring bank, a security risk is created. Though, many banks offer systems where encrypted card facts captured on a merchant's web server can be sent straight to the payment processor.
Controlled Payment Numbers are one more alternative for protecting one's credit card number: they are "alias" information linked to one's actual card number, produced as needed, valid for a comparatively short time, with a very low limit, and classically only suitable with a single merchant.
The Federal Bureau of inquiry and U.S. Postal assessment Service are responsible for prosecuting criminals who connect in credit card fraud in the United States, but they do not have the possessions to follow all criminals. In common, federal officials only prosecute cases more than US $5000 in value. Three enhancements to card security have been initiated to the further ordinary credit card networks but none has verified to help reduce credit card deception so far. Initial, the on-line authentication system used by merchants is being improved to require a 4 digit Personal Identification Number (PIN) known only to the card holder. Second, the cards themselves are being substitute with similar-looking tamper- resistant smart cards which are intended to make forgery more difficult. The bulk of smartcard (IC card) based credit cards comply with the EMV (Euro pay MasterCard Visa) standard. Third, an supplementary 3 or 4 digit code is now at hand on the back of most cards, for make use of in "card not present" transactions. See CVV2 for further information.
The technique credit card owners pay off their balances has a marvelous outcome on their credit history. All the information is collected by credit bureaus. The credit information keeps on on the credit report, depending on the authority and the circumstances, for 1, 2, or even 10 years after the debt is repaid.