Q. Write down the binary search algorithm and trace to search element 91 in following given list:
13 30 62 73 81 88 91
What are the major limitations of Binary Search?
Ans.
13 30 62 73 88 91
lets us store the numbers in an array
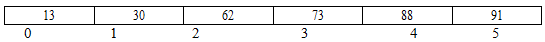
To start with we take low = 0 and high = 5 hence mid = (low+high)/2 = (0+5) /2 = 2
since a[mid] = a[2] = 62 ≠ 91 and low < high we go to next iteration as 62 < 91
∴we take low = mid+1 = 3 and high =
now we find mid =( 3+5)/2 = 4
∴a [mid] = a[4] = 88.
88 is not equal to 91
again 88< 91
∴ we take low = mid +1 = 4 + 1 = 5 and high = 5
∴mid = (5+5)/2 = 5
∴ a[mid] = a[5] = 91 which is the search element.
Limitation of Binary Search is given below: -
(i) The complexity of Binary search is O(log2 n) the complexity is same irrespective of the location of the element, even if it is not there in the array.
(ii) The algorithm makes an assumption that one has direct access to middle element in the list on a sub list. This means that the list must be stored in some type of array. Unfortunately inserting an element in an array requires element to be moved down the list and deleting an element from an array requires element to be moved up the list.
(iii) The list must be sorted.