Reference no: EM13997758
Q1) Make use of the Network below, use Dijkstra's algorithm and compute the shortest path from x to all network nodes. Show how the algorithm works by computing a table similar to the following:
| Step |
N' |
D(v),p(v) |
D(w),p(w) |
D(x),p(x) |
D(y),p(y) |
D(z),p(z) |
| 0 |
u |
2,u |
5,u |
1,u |
|
|
| 1 |
ux |
2,u |
4,x |
|
2,x |
|
| 2 |
uxy |
2,u |
3,y |
|
|
4,y |
| 3 |
uxyv |
|
3,y |
|
|
4,y |
| 4 |
uxyvw |
|
|
|
|
4,y |
| 5 |
uxyvwz |
|
|
|
|
|
Let us define the following notation:
• D(v): cost of the least-cost path from the source node to destination v as of this iteration of the algorithm.
• P(v): previous node (neighbor of v) along the current least-cost path from the source to v.
• N: subset of nodes: v is in N' if the least-cost path from the source to v is definitively known.
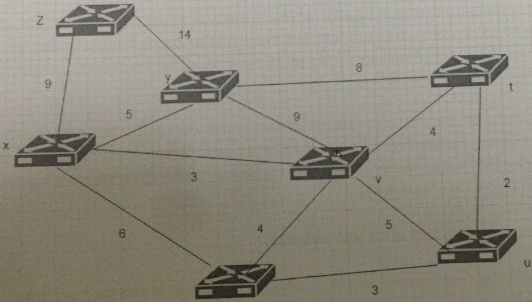
Q2) Consider the network shown in Problem P26. Using Dijkstra's algorithm, and showing your work using a table similar to the table shown in QI , do the following:
a. Compute the shortest path from t to all network nodes.
b. Compute the shortest path from u to all network nodes.
c. Compute the shortest path from v to all network nodes.
d. Compute the shortest path from w to all network nodes.
e. Compute the shortest path from y to all network nodes.
f. Compute the shortest path from z to all network nodes.
Q3) The CS department at Saint Andrew University bought new Sun Fire V210 servers. They decided to run a distance-vector protocol for routing between these servers (even though it is a rather small network). They are currently configured as the picture below, with respective edge costs.
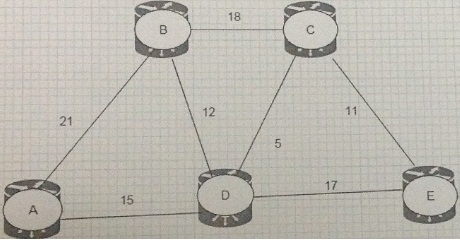
The CS staff asked for your help. Write down each step of bdilding the distance vector routing table for 'E' so they can compare it to the output of their implementation.
Q4) From a service perspective, explain by giving two examples what is an important difference between a smmetric-key system and a public-key system?
Q5) Neverland's Immigration Department is to send a sequence of photograph over Ethernet cable for identification purposes, The photograph size is 591x827 pixels, each pixel is 26 bits. The rate of sending is 80 photographs per second. The bandwidth of the channel is 12 Hz. Assuming white thermal noise, using Shannon's formula. calculates what signal-to-noise ratio is required to achieve this capacity?
Q6) For the bit stream 0100110011101010, sketch the waveforms for each of the codes NRZ-L, NRZ-I, Bipolar-AMI, Manchester and Differential Manchester. Assume that the signal level for the preceding bit for NRZ-1 was high; the most recent preceding 1 bit (Bipolar-AMI) has a negative voltage. The previous signal flow from negative to positive voltage in Differential Manchester Digital Encoding Schemes
7) Explain in detail how Data Encryption Standard works with a diagram.
8) What are the differences between message confidentiality, integrity, availability, authentication? Can you have one without the other? Justify your answer by giving an example.
|
How integrated is this company communication
: Describe the company's corporate communication in terms of its corporate identity, image and reputation write an essay of approximately 1000 - 1500 words that answers the following questions. ?In your experience, how integrated is this company's c..
|
|
What imply classical aggregate supply curve would look like
: Classical economists assumed that wage rates, prices, and interest rates were flexible and would adjust quickly. Consider an extreme case: Suppose classical economists believed wage rates, prices, and interest rates would adjust instantaneously. ..
|
|
Elite plc
: Write a report, addressed to the board of directors of Elite PLC, commenting on the performance of the company for the year ended 31 December 2015 and give possible explanations for the differences between the business's actual performance and its bu..
|
|
Social media and social commerce
: You are required to write a report (1500 – 2000 words) to explain the concepts of social media and social commerce and assess how they can be used to assist in meeting the strategic objectives of a Hotel.
|
|
Compute the shortest path from x to all network nodes
: What are the differences between message confidentiality, integrity, availability, authentication? Can you have one without the other? Justify your answer by giving an example.
|
|
How long would simple seconds pendulum be at same location
: A simple pendulum 89.5cm in length requires 10.70 minutes to make 285 complete swing. how long would a simple seconds pendulum be at the same location?
|
|
What is the frequency of the oscillation in hz
: A simple pendulum consists of a mass 1.72 kg hanging from a light cord of length 66 cm. The mass is displaced to one side and released. Using g = 9.8 m/s2, what is the frequency of the oscillation in Hz? Express your result to three significant di..
|
|
Calculate the ratio of the speed of the moon
: The present period is 2.36 x 106 s. Assume that the orbit of the Moon is circular. Calculate the ratio of the speed of the Moon in its ancient orbit to the speed that it has today.
|
|
Determing the length of the pendulum
: Then, the pendulum is brought to planet X (which is smaller than Earth), and now takes 1.151 seconds for the pendulum to swing from one turning point to the other turning point. Determing the length of the pendulum, the acceleration of gravity on ..
|