Reference no: EM13824933
Question 1: Protocol Analysis with Wireshark
This assignment question requires that you analyse a packet capture dump file and provide comments explaining each packet. This pcap file contains a SMTP transaction between a client and server. Your task is to annotate each packet commenting on the following characteristics.
• Comment on any significant TCP flags and what they mean in the context of the packet capture. Significant flags include SYN, FIN, RST, and URG. You must explain why the flag has been set and what it means for this TCP connection.
• Comment on the direction of each packet (ie. client -> server or server -> client). Be clear to explain in which direction the interaction is occurring.
• Comment on each SMTP command and response between the client and the server. You must explain what each command does. You should also explain the data that is exchanged. This will require that you study the SMTP RFC or other Internet documents relating to SMTP to understand what the commands mean.
You should also comment on the 2 port numbers used in this connection and their significance. For example, is it an ephemeral or reserved port? If it is a reserved port, what protocol does it relate to?
On the following page is an example of the template to use to complete this question. It provides a brief summary of each packet and has been formatted to include an "explanation" field underneath each packet. You are to write your comments in this "explanation" field addressing the packet immediately above, based on your analysis of the packet using Wireshark. Be specific and detailed. Any vague or limited responses will not attract any marks. Note, that the table is only a summary of the information provided in the pcap file. Be sure to comment in relation to information provided in the pcap file using Wireshark, not just the summary table.
For examples of how to complete the table, be sure to have completed all 3 parts of the Packet Capture Exercises. They are available from the Lectures and Tutorials page of the course website. Your solution must of course be in your own words. Do not copy directly from any examples or you will get zero marks
Question 2: Firewall and Proxy Services Configurations
The following diagram shows the topology of the network of a small company. There are three servers located in a DMZ (Demilitarised Zone).
The web server can directly accept requests (HTTP or HTTPS) from the Internet or from the internal network (192.168.1.0/25).
The DNS server can directly accept requests from the Internet. The DNS server can also directly accept requests from the internal network (192.168.1.0/25). However, if the DNS server can not resolve a domain name requested by the internal network (192.168.1.0/25), it will contact the DNS servers on the Internet directly for the name resolution.
On behalf of the users on the internal network (192.168.1.0/25), the email server sends emails to and receives emails from the Internet. The users on the internal network (192.168.1.0/25) use IMAP (Internet E-mail Access Protocol) to read and organise their emails on the email server.
The users on the internal network (192.168.1.0/25) are allowed to access the Internet only for HTTP, HTTPS and FTP services. However, the users of the internal network are never allowed to connect to the Internet directly.
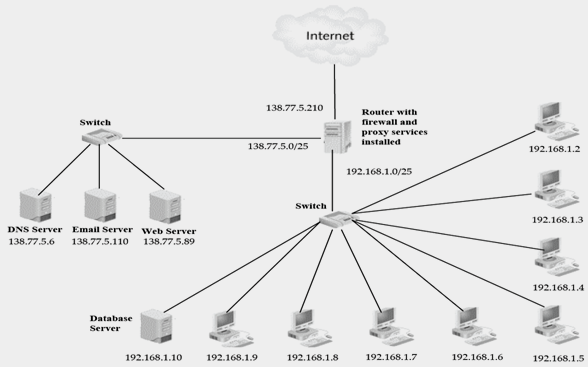
Based on the above network configuration and application scenarios, answer the following three questions.
A. The firewall services are installed on the router. Create the firewall rules to implement the packet filtering and only allow the specified traffic. The firewall rules are to be created in the following format.
|
Rule No.
|
Application Protocol
|
Transport Protocol
|
Source IP
|
Source Port
|
Destination IP
|
Destination Port
|
Action
|
|
1
|
|
|
|
|
|
|
|
|
2
|
|
|
|
|
|
|
|
|
:
|
|
|
|
|
|
|
|
|
:
|
|
|
|
|
|
|
|
|
:
|
|
|
|
|
|
|
|
B. Briefly explain each rule in the rule base that you have created.
C. The proxy services are also installed on the router to conceal the users of the internal network (192.168.1.0/25) from the Internet. Suppose that users on the internal computers send the following requests to the Internet. The proxy services perform the Port Address Translation (PAT). Complete the following connection table to show how PAT is working for requests from the users on the internal network.
|
Packet Addressing on internal network
|
Packet Addressing on external network
|
|
Source IP
|
Source Port
|
Destination IP
|
Destination Port
|
Source IP
|
Source Port
|
Destination IP
|
Destination Port
|
|
192.168.1.2
|
1033
|
203.206.209.77
|
80
|
|
|
|
|
|
192.168.1.2
|
1035
|
210.10.102.196
|
443
|
|
|
|
|
|
192.168.1.5
|
2301
|
203.206.209.55
|
21
|
|
|
|
|
|
192.168.1.5
|
2302
|
202.2.59.40
|
443
|
|
|
|
|
|
192.168.1.5
|
4123
|
72.5.124.55
|
80
|
|
|
|
|
|
192.168.1.8
|
4128
|
72.5.124.35
|
21
|
|
|
|
|
|
192.168.1.8
|
1033
|
150.101.16.250
|
80
|
|
|
|
|
|
192.168.1.9
|
1035
|
150.101.16.250
|
443
|
|
|
|
|
Question 3: Network Attack Research
Although the course textbook and other resources discuss several specific network attack vulnerabilities, it is not feasible to cover all of them. New vulnerabilities are being discovered all of the time, and there are hundreds of currently known vulnerabilities. Professional network administrators have to keep themselves current with all possible threat possibilities. One way of doing this is by performing personal research. In this hypothetical case study, you should use the Internet to assist you in developing responses to the three questions. Use of the course textbook and supplied resources only is not sufficient to award full marks. You should use your research skills and go beyond these resources.
PHP is a popular scripting language commonly used to implement dynamic web pages. Unlike JavaScript, which is a web client-side scripting language, PHP is a web server-side scripting language. At the web server, PHP scripts are used to dynamically generate the HTML pages that are then sent to the client. At the client end these HTML pages are displayed in the web browser.
James has just completed his first year at university in a Bachelor of Information Technology degree. One of the courses that James studied was Web Programming 101. In that course James learnt the basics of using HTML, CSS and PHP to create dynamic web pages.
As a favour to James' good friend Kirandeep, he designed and implemented a simple dynamic blog site using the skills he had gained in Web Programming 101. After testing the web site on a local secure network, and fixing a number of scripting errors. James delivered the implementation files to Kirandeep, who uploaded them to an ISP web hosting site. Both James and Kirandeep were ecstatic to see people from across the Globe using the web site to share their personal experiences.
Within a few hours of the blog site going live, Kirandeep received an urgent email from the ISP Manager informing her that the blog site had to be closed down because it had been used by unknown hackers to send spam emails to thousands of addresses around the world. The Manager told Kirandeep that she could only reactivate the blog site when the problem had been fixed and it could be guaranteed that it would not happen again.
Kirandeep quickly phoned James and told him of the dilemma. James spent the rest of the day and most of the next night examining his PHP scripts and doing research on the Internet to find out what might have caused the problem. After many hours James tracked the problem down to the simple web page contact form that he had used so that people could send emails to Kirandeep without letting them know what Kirandeep's email address was.
Users fill out the form by supplying their email addresses, a brief subject line, followed by the message to be sent to Kirandeep. When the submit button is clicked, the contents of the form fields are sent to the web server, where a PHP script receives the field information and uses it to initiate an email to Kirandeep. Kirandeep's email address is stored in the PHP script, so the form user never gets to see it. That way Kirandeep's email address is kept secret. Unknown to James, the use of simple contact forms is a well-known vulnerability that threat agents can exploit. He also discovered that it is not only PHP scripts that are vulnerable to this type of exploitation - all of the several available server-side scripting languages are vulnerable.
You are required to answer the following questions. Please reference all sources - do not copy directly from sources.
a) Based on the information provided, what type of attack has been performed by the hackers using Kirandeep's blog? You need to fully justify your answer, not just state the type of attack.
b) Describe in detail how the attack may have occurred - you will need to provide sample form field data such as:
Your Email Address: M.Patel@hotmail .com
Subject: Thank you
Message: Thank you for providing such a useful blog site for me to use. I have learnt a lot from reading the blogs left by other people.
You don't need to provide a detailed explanation of how PHP or other server-side scripting languages work; but you need to provide sufficient information to explain how malicious field data entered by a hacker could trick the web server into generating multiple spam emails.
c) How would James need to change the PHP script to prevent such attacks? You don't need to provide the actual PHP code - just describe what measures James would have to implement to ensure that malicious field data could not be used to generating multiple spam emails.
d) What limitations does this form of attack have?
Question 4:
In this hypothetical case study, you should use the Internet to assist you in developing responses to three questions. Use of the text only is not sufficient to attract full marks.
SafeBank recently received a series of reports from customers concerning security breaches in online banking. Customers reported having money transferred from their accounts, usually after they have found that their password has changed. A full security audit revealed that the money transfers and changes to user passwords all originated from an Eastern European country on servers within the domain of crazyhackers.com - however - the question remained: how did the hackers undertake the attack?
Given that legitimate account numbers and passwords were used, it was initially assumed that it could be some form of phishing attack. However, no evidence of such emails was found. The only commonality between the victims was that they all used the same ISP.
You are required to answer the following questions. Please reference all sources - do not copy directly from sources.
A. Based on the information provided, what type of attack has been performed? Justify your answer.
Hint: In order to capture account numbers and passwords, how would a hacker "redirect" users to their servers instead of SafeBank's?
B. Describe in detail how the attack occurred - you may wish to include one or more diagrams. You will need to make assumptions about host names, domains and IP addresses - document these. You need not concern yourself with the technical details of the capture and reuse of SafeBank's customer details (eg. Fake web sites/malware) - you are documenting how it was possible from a network perspective.
C. What steps would you advise to prevent such attacks? What limitations does this form of attack have?