Reference no: EM131149930
Assignment: VLAN Troubleshooting
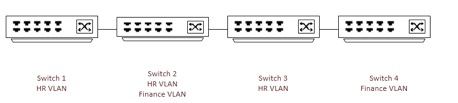
XYZ Company is a very large retail chain in the Midwest United States. This company operates with a single corporate campus location and 25 regional distribution centers that support 3,000 retail locations. XYZ Company recently deployed a new switching environment using Virtual Local Area Network (VLAN) and Spanning Tree technology. The new switching environment includes redundant connections between each switch and includes the HR and Finance VLANs as shown below. Devices plugged into the HR VLAN on any switch require access to the HR VLANs across all switches. Devices plugged into the Finance VLAN require access to the Finance VLANs across all switches.
There have been multiple problems reported with the VLAN and Spanning Tree switching environment.
The new switching environment has exhibited the following problems:
• Switch 1 HR VLAN communication cannot take place with Switch 2 HR VLAN
• Switch 2 Finance VLAN cannot communicate with Switch 4 Finance VLAN
• Switch 4 has both trunk ports to switch 3 continuously going from blocking to forwarding
• Root bridge election is occurring every minute
You were brought in based on your troubleshooting knowledge to address the issues.
Write a two to four page paper in which you:
1. Decide the troubleshooting methodology that you would use for each issue. Provide a rationale to support your response.
2. Provide the main steps that you would use to troubleshoot each of these issues and determine the tools that you would require to complete your troubleshooting. Provide a rationale to support your response.
3. Speculate on the main cause(s) of each of the four problems. Provide a rationale to support your response.
4. Use at least two quality resources in this assignment. Note: Wikipedia and similar Websites do not qualify as quality resources.
Your assignment must follow these formatting requirements:
• Be typed, double spaced, using Times New Roman font (size 12), with one-inch margins on all sides; citations and references must follow APA or school-specific format. Check with your professor for any additional instructions.
• Include a cover page containing the title of the assignment, the student's name, the professor's name, the course title, and the date. The cover page and the reference page are not included in the required assignment page length.
The specific course learning outcomes associated with this assignment are:
• Describe and develop maintenance methods and processes and procedures through the use of networking tools, resources, and techniques.
• Summarize and develop troubleshooting processes for enterprise networks.
• Use technology and information resources to research issues in internetworking troubleshooting.
• Write clearly and concisely about internetworking troubleshooting using proper writing mechanics.
|
What will be the value of matt''s account in ten years
: What will be the value of Matt's account in ten years with his monthly payments if he is earning 6% (APR), 8% (APR) or 12% (APR)?
|
|
Develop a test program that triggers a change
: Develop a test program that triggers a change in the statistics above, report them on standard output - Replace the second-chance LRU approximation algorithm in both the active and inactive lists with a counter-based clock algorithm.
|
|
Conduct an organizational assessment on the dhl company
: Conduct an Organizational Assessment on the DHL COMPANY AND DHL and its global competitiveness. The aim of this assignment is to examine the business strategy of the World famous logistic company-DHL and its global competitiveness. It has gained the..
|
|
Create portfolio of local suppliers for his new line
: Phillip Witt, president of Witt Input Devices, wishes to create a portfolio of local suppliers for his new line of keyboards. As the suppliers all reside in a location prone to hurricanes, tornadoes, flooding, and earthquakes, Phillip believes that t..
|
|
Provide the main steps that you would use to troubleshoot
: Provide the main steps that you would use to troubleshoot each of these issues and determine the tools that you would require to complete your troubleshooting. Provide a rationale to support your response.
|
|
Find the fundamental frequency for the lateral vibration
: Using Rayleigh s method, find the fundamental frequency for the lateral vibration of the beam shown in Fig. 8.39. The restoring force in the spring k is proportional to the deflection, and the restoring moment in the spring is proportional to the ..
|
|
How do ethics and culture affect your decision
: What negotiation strategy do you use to support the school board's need to redraw the boundaries while addressing the concerns of the stakeholders? How do ethics and culture affect your decision
|
|
What consequences does have on the traction conditions
: Pick five different cars. Determine what sort of differentials they have. What consequences does this have on the traction conditions on different surfaces (ice, etc)?
|
|
What are your assigned company geographic markets
: What are the products / services that your firm is offering and what are the benefits to its targeted external customers? Which customer segments is your assigned company targeting? What are your assigned company geographic markets (from it's geograp..
|