Reference no: EM131267222
Objectives:
The main objective of this assignment is for the students to understand the security mechanisms in Unix-like operating systems and their interplay with software security, in particular:
- to learn practical access control mechanisms in Unix operating system, such as files and folder permissions and SUID programs, and how application security is affected by them;
- to learn how software vulnerabilities can be exploited to circumvent security mechanisms in both applications and operating systems.
Problem Description:
There are three problems in this assignment. To do this assignment, you will make use of an installation of Ubuntu Linux 12.04 (32 bit) in the Oracle VirtualBox virtual machine. The VirtualBox image of the Ubuntu installation is provided with this document and can be downloaded from the NTULearn site for this assignment, under the Group assignment menu. The assessment of the solutions to the problems listed below will be entirely done inside this particular installation of Ubuntu.
The Ubuntu installation for this assignment is a clone of the Ubuntu image provided for the tutorial sessions. In particular, it has the following users: admin, alice, bob, charlie, dennis, eve and fong.
User admin has the administrative privilege over the system, i.e., it can escalate its privilege to the root user.
The user bob maintains several applications that allows a user to access a certain ‘secret', when the right password is provided. These passwords are different from the user account passwords. To distinguish the two, we shall call these passwords as application passwords. Every user is assigned a unique secret and a unique application password. The secrets take the form of a string of alpha numeric characters. The application passwords and the secrets are stored in individual files. The locations for these files are summarized in Table 1. The application passwords are strings of lower- case letters, of length at most 14 characters.
IMPORTANT NOTE: Appendix A provides the account passwords, the application passwords and the secrets for all users. All these passwords and secrets, except those for user ‘charlie', will be changed during the assessment of your solutions. So your solutions must not hardcode any of these passwords and secrets other than charlie's.
|
User name
|
Application password file location
|
Secret file location
|
|
admin
|
/home/admin/Private/password
|
/home/admin/Private/secret
|
|
alice
|
/home/bob/Private/alice/password
|
home/bob/Private/alice/secret
|
|
bob
|
/home/bob/Private/bob/password
|
home/bob/Private/bob/secret
|
|
charlie
|
/home/bob/Private/charlie/password
|
home/bob/Private/charlie/secret
|
|
dennis
|
/home/bob/Private/dennis/password
|
home/bob/Private/dennis/secret
|
|
eve
|
/home/bob/Private/eve/password
|
home/bob/Private/eve/secret
|
|
fong
|
/home/bob/Private/fong/password
|
home/bob/Private/fong/secret
|
Table 1. Locations of application passwords and secrets. Each password is stored in a file called ‘password', and each secret is stored in a file called ‘secret'.
There are three main programs that a user can use to display his or her secret:
- user-secret: This program is used to access the secrets for the following users only: alice, charlie, dennis, eve and fong. It takes two arguments: a user name and an (application) password. If the application password supplied is correct for that user, the secret for the user will be displayed. The following screenshot shows an example of the output of a normal run of the program.
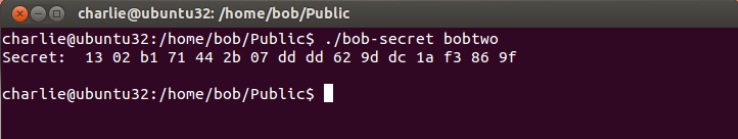
- bob-secret: This program is used by user bob to access his secret. It takes one argument, which is bob's application password. If the password is correct, bob's secret will be displayed. The following screenshot shows an example of the output of a normal run of the program.
- admin-secret: This program is used by user admin to access its secret. It takes one argument, which is admin's application password. If the password is correct, admin's secret will be displayed. The following screenshot shows the output of a normal run of the program.
In addition to the above three programs, there are additionally two helper programs:
- show-secret: This program is invoked by bob-secret to display bob's secret, in case of a successful authentication check. It is not supposed to be invoked by the users directly.
- register: This program is invoked by bob-secret to display an error message in case of an unsuccessful authentication check. It is not supposed to be invoked by the users directly.
All of the above programs, except for register, are SUID programs. Table 2 lists the locations of the binaries of the programs. The source code of these programs are written in C and are located in the same directory as their binaries. For your convenience, the source code of these programs are included in Appendix B.
There are further details about the permissions of each program above that you need to discover on your own. Pay particular attention to the SUID programs and their owners.
Table 2. Program locations
There are 3 (three) problems you need to solve for this assignment. For each problem, you are asked to write an attack program or script. These attack programs/scripts must be executed using user charlie's account. So in the following, we assume all attack programs/scripts are located in
/home/charlie/.
Problem 1
Your first task is to write an attack script or a program to display the secret of any of the following users: alice, charlie, dennis, eve, or fong. The attack program takes one argument, which is the user you want to attack. The attack must work when executed by user charlie. If your program/script works correctly, it should show something that looks like the following:
That is, each successful attack should display the word ‘Secret: ‘, followed by a string that is the secret.
Problem 2
For this problem, you are asked to write an attack script/program to display bob's secret. The attack program takes no argument. As in Problem 1, this attack must work when launched by user charlie. The following screenshot shows what a successful attack should look like:
Problem 3
For Problem 3, you are asked to write a script/program to display the application password and the secret of the admin user. The attack program takes no argument. A successful attack should output something like the following:
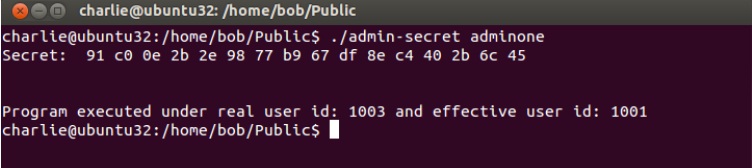
Again, as in previous problems, this attack must be successfully executed when logged in as charlie.
The attack should output two lines: the first one contains the application password (the line prefixed by ‘Password:') and the second one contains the secret of the admin user (the line prefixed with ‘Secret:').
Assessment
The assessment is based on two components:
1. Attack code execution: This is broken down to 15% for Problem 1, 15% for Problem 2 and 20% for Problem 3. The assessment of the correctness of your attack will be partially automated, so please make sure you follow the suggested output format as mentioned in the problem description above. Your solutions will be tested in the same virtual machine that is provided with this assignment, but with all password and secret values modified (except for charlie's passwords and secret). So you should make sure that you do not hardcode any of the sample passwords/secrets, other than charlie's, mentioned above in your solutions, as they will not work in the assessment process. Each attack must be successfully executed within 2 (two) minute. This is really a gross approximation; if you implement the attacks correctly, each attack should take only a few seconds to solve the given problem.
2. Report- There is no definitive structure of the report, but here are some guidelines of what we would expect from the report:
- As a general guideline we expect a division into three parts, corresponding to the division of the problems. But if you are able to find a single attack that solves all problems, in which case, the division per problem does not work so well and the report will be judged more holistically.
- We expect a detailed analysis of what are the vulnerabilities and how you exploit them. It is not enough, for example, to say that you do a ‘stack overflow' attack. You'd need to explain about the memory layout, what is the effect of the overflow, how do you subvert the control flow of the program, etc. Similarly, where the problem/solution concerns Unix security mechanism, I expect you to articulate clearly the aspects of the control mechanism that cause the vulnerability, and how you exploit them.